Digital INSECURITY
Breaking News, July 18, 2021 —
Israeli spyware maker NSO ensures no mobile phone is safe and secure.
The New York Times reported today that NSO Group’s “Pegasus” product documentation states that its spyware tech allows for “unlimited access to a target’s mobile devices.”
The company’s promotion claims include its technology can …“remotely and covertly collect information about your target’s relationships, location, phone calls, plans and activities — whenever and wherever they are.” And, “It leaves no traces whatsoever.”
The NSO Group further asserts that its tracking software and hardware can install itself in any number of ways, including “over the air stealth installation,” and is tailored to text messages and emails, through public Wi-Fi hot spots where NSO software is secretly installed and activated.

For the last six years, the NSO Group’s surveillance and tracking system Pegasus, has been used by a growing number of government agencies around the world to target a range of smartphone users — including iPhones, Androids, and BlackBerry and Symbian systems — and without leaving a trace.
Data leaked suggests the powerful cyberespionage tool is enabling governments to spy on and target news organizations, rights activists, dissidents, journalists, opposition politicians, political dissidents, and academics.
Although such intelligence gathering capabilities have played an integral part for intelligence agencies of United States, Russia, China, Britain, and the EU, what set’s NSO apart is its technology sales to anyone who can pay, including authoritarian regimes that use the spyware for purposes that go far afield of the company’s stated aim: targeting terrorists and criminals
The Pegasus software has been deployed against journalists, rights campaigners and policymakers in Azerbaijan, France, Hungary, India, Morocco. Bahrain, Mexico, Morocco, Saudi Arabia and the U.A.E.
To learn more about the Pegasus spyware, and its potential relationship to your phone, view this two minute video: https://youtu.be/2iQuk3p95M8
Originally Reported, July 6th, 2021 —
Ransomware hackers demand $70m, over 1,500 businesses attacked
The hackers who claimed responsibility for this latest global security breach demanded $70m to restore all the affected businesses’ data, if the targeted retail and medical services victims wanted to mitigate the economic harm of extended business disruptions.
After the recent major oil-gas pipeline disruption impacting most of the US east coast fossil fuel supplies, the White House said this week they were “checking to see whether there was any “national risk” posed by this most recent cyber attack targeting retailers. So far there is no evidence of any nationally important organizations being impacted — at this time.
Today we live with the threat of digital attacks and data breaches defined within one of more of these four categories:
- State-sponsored attacks designed to disable and disrupt their target countries and gathering intelligence, e.g. the United States, China, Russia, Iran and Israel
- Commerce-directed attacks designed to extort money and inflict economic harm (as in this latest reported attack)
- Intellectual property theft, historically led by state actors, e.g., China and Russia, and affiliated or independent organized crime entities
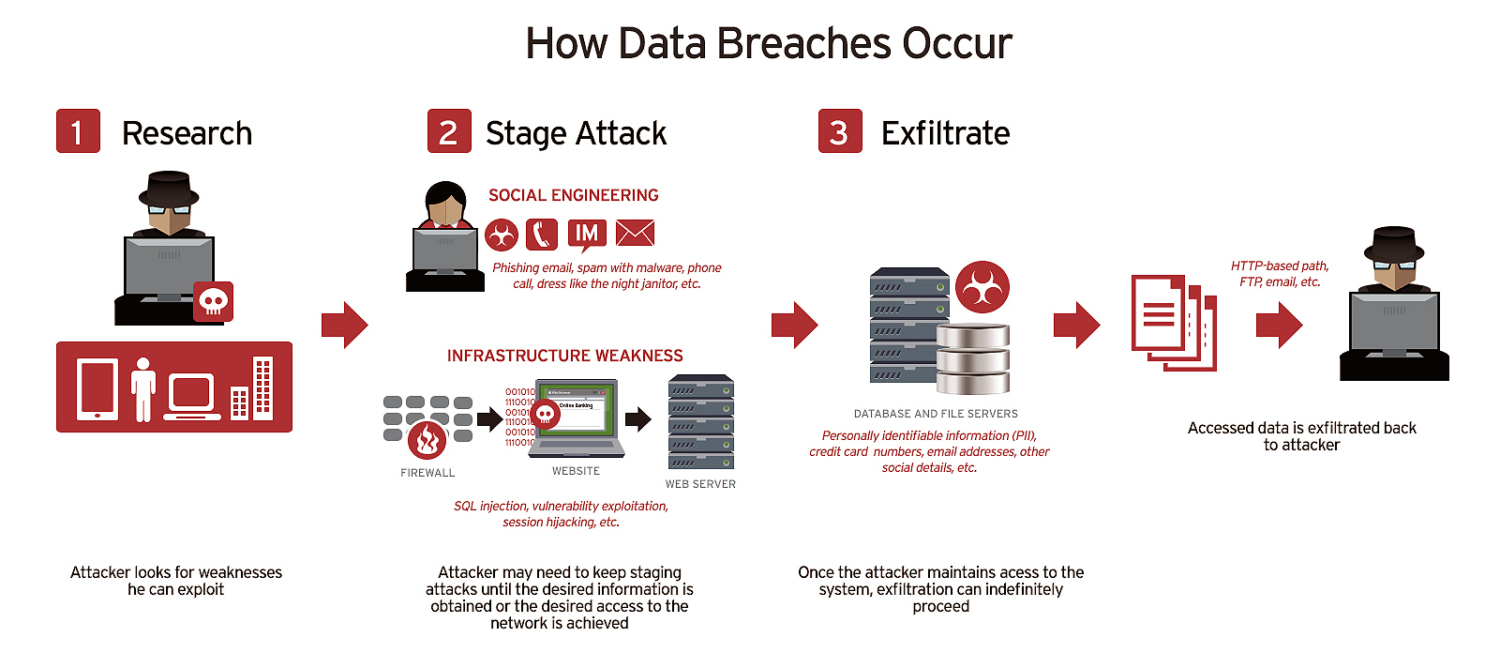
- Data breaches designed to steal personal and private consumer information from presumably secure private and public sector data warehouses
~ In this article we explore the vulnerabilities most Americans face as participants in a world gone digital ~
Major Private Sector Computer Breaches
It is the latter data breaches this article is focused on — the type of information theft that affects the daily lives and credit ratings of anyone connected to the Internet. Not long ago, a breach that compromised the data of a few million people would have been big news. Now, breaches that affect hundreds of millions or even billions of people are far too common.
About 3.5 billion people saw their personal data stolen in the past 10 years.

The smallest incident on this list involved the data of a mere 134 million people.
eBay reported an attack exposed its entire account list of 145 million users in May 2014, including names, addresses, dates of birth and encrypted passwords.
Yahoo announced in September 2016 that in 2014 it had been the victim of what would be the biggest data breach in history. The attackers, which the company believed we “state-sponsored actors,” compromised the real names, email addresses, dates of birth and telephone numbers of 500 million users. Yahoo revised that estimate in October 2017 to include all of its 3 billion user accounts.
Four years ago Equifax made headlines for the exposure of private information of millions of people.
Equifax, one of the largest credit bureaus in the US, said on Sept. 7, 2017 that an application vulnerability in one of their websites led to a data breach that exposed about 147.9 million consumers. The breach was discovered on July 29, but the company says that it likely started in mid-May. The breach compromised the personal information (including Social Security numbers, birth dates, addresses, and in some cases drivers’ license numbers) of 143 million consumers; 209,000 consumers also had their credit card data exposed. That number was raised to 147.9 million in October 2017.
Marriott International announced in November 2018 that attackers had stolen data on approximately 500 million customers. The breach initially occurred on systems supporting Starwood hotel brands starting in 2014. The attackers remained in the system after Marriott acquired Starwood in 2016 and were not discovered until September 2018.
The attackers were able to take some combination of contact information, passport number, Starwood Preferred Guest numbers, travel information, and other personal information. The credit card numbers and expiration dates of more than 100 million customers were believed to be stolen. The breach was eventually attributed to a Chinese intelligence group seeking to gather data on US citizens, the New York Times reported.
The 15 biggest private sector data breaches in recent history, (publicly revealed):
- Adobe
- Adult Friend Finder
- Canva
- Dubsmash
- eBay
- Equifax
- Heartland Payment Systems
- Marriott International
- My Fitness Pal
- MySpace
- NetEase
- Sina Weibo
- Yahoo
- Zynga — Once a giant of the Facebook gaming scene, Farmville creator Zynga is still one the biggest players in the mobile game space with millions of players worldwide. The hack stole account information from Zynga’s database of Draw Something and Words with Friends players to the 218 million accounts. Zynga later confirmed that email addresses, salted SHA-1 hashed passwords, phone numbers, and user IDs for Facebook and Zynga accounts were stolen.
Major Public Sector Computer Breaches
The U.S. (federal) government agencies to state agencies have also been targets of cyber attacks and information theft, revealing to attackers millions of U.S. citizens’ private information through every level of government.
Here’s a list from smallest to largest in terms of the number of individuals affected, the 10 biggest government data breaches include:
- 10. State of Texas: 3.5 Million Affected (April 2011)
- 9. South Carolina Department of Revenue: 3.6 Million Affected (October 2012)
- 8. Tricare: 4.9 Million Affected (September 2011)
- 7. Georgia Secretary of State Office: 6.2 Million Affected (November 2015)
- 6. Office of the Texas Attorney General: 6.5 Million Affected (April 2012)
- 5. Virginia Department of Health Professions: 8.3 Million Affected (May 2009)
- 4. U.S. Office of Personnel Management (OPM): 21.5 Million (June 2015)
- 3. U.S. Department of Veteran Affairs: 26.5 Million Affected (May 2006) – A suspected Russian attack
- 2. National Archives and Records Administration (NARA): 76 Million Affected (October 2009)
- 1. U.S. Voter Database: 191 Million Affected (December 2015) – A Russian attack was suspected and likely, just ahead of the 2016 Presidential election.
Since 2020 …
Last year, we also began to see the Federal Trade Commission (FTC) impose hefty fines and penalties on organizations, such as those relating to the Equifax breach and Facebook data leaks, to settle charges of improper handling of Personally Identifiable Information (PII).
According to the Identity Theft Resource Center, the overall number of data breaches affecting Americans is even higher, reporting more than 1,108 breaches in the United States in 2020 alone.
There was a whirlwind of scams and fraud activity in 2020. Data breaches continue to expose consumers’ Personally Identifiable Information (PII) at an alarming rate, putting close to three hundred million people at risk of identity theft and fraud. Cybercriminals are also focusing their time on other lucrative cyberattacks, such as ransomware, credential stuffing, malware, and Virtual Private Network (VPN) exploitation.
January 11, 2021: A Chinese social media management company, Socialarks, suffered a data leak through an unsecured database that exposed account details and Personally Identifiable Information (PII) of at least 214 million social media users from Facebook and Instagram, and LinkedIn.
Researchers from the University of Michigan School of Information showed 413 people facts from up to three breaches that involved their own personal information. The researchers found people were not aware of 74% of the breaches. “This is concerning. If people don’t know that their information was exposed in a breach, they cannot protect themselves properly against a breach’s implications, e.g., an increased risk of identity theft, says doctoral candidate Yixin Zou.
How does all this affect me?
The Have I Been Pwned database engaged in a recent study of global cyber attacks and lists nearly 500 online breaches over the last decade.
According to the Identity Theft Resource Center, the overall number of data breaches affecting Americans is even higher, reporting more than 1,108 individual data breaches in the United States in 2020 alone.
Of all information that was breached, email addresses were compromised the most, followed by passwords, usernames, IP addresses, and dates of birth.
Most participants expressed moderate concern and were most worried about the leak of physical addresses, passwords, and phone numbers. In response to their compromised accounts, they reported taking action or an intention to change passwords for 50% of the breaches.
“It could be that some of the breached services were considered ‘not important’ because the breached account did not contain sensitive information. However, low concern about a breach may also be explained by people not fully considering or being aware of how leaked personal information could potentially be misused and harm them,” says Peter Mayer, postdoctoral researcher at Karlsruhe Institute of Technology.
Risks range from credential stuffing—or using a leaked email address and password to gain access to other accounts of the victim—to common identity theft and fraud.
Most of the breaches never made the news, and often they involved little or no notification to affected individuals. “Today’s data breach notification requirements are insufficient,” Zou says. “Either people are not being notified by breached companies, or the notifications are crafted so poorly that people might get an email notification or letter but disregard it. In prior work, we analyzed data breach notification letters sent to consumers and found that they often require advanced reading skills and obscure risks.”
What Should I do when (not if) my personal information has been digitally stolen?
- Check whether accounts were part of a breach using free services such as https://haveibeenpwned.com/ or https://monitor.firefox.com/.
- Read breach notifications carefully.
- Websites like the FTC’s https://identitytheft.gov/ can help create a recovery plan after identity theft.
- Make sure to change the password of the breached account and any others for which the same password was used. Doing this once should be enough unless there is a new breach.
- Sign up for identity monitoring services you get offered. Though not perfect, they are better than nothing.
- If you experience actual harm from a breach you may also be entitled to further support.
- To prevent future data breaches:
- Use a unique password for each online account. No one can remember dozens of these so it’s best to use a password manager to store and create strong passwords.
- Use two-factor authentication, wherever possible, that requires a code by phone in addition to a username and password in order to access an account.
- Freeze credit reports at the three major bureaus (Equifax, Experian, and TransUnion) to make it more difficult for identity thieves to cause financial harm.
For more information on this subject, see the April 2021 BeyondKona article “A 21st Century Power Struggle: bombs are out, bots are in” which explores state-sponsored cyberwarfare and the consequences of this new kind of bullet-less warfare.




Leave a Reply
Join the Community discussion now - your email address will not be published, remains secure and confidential. Mahalo.